Homepage:
https://wordpress.org/plugins/simple-personal-message/
Description:
Type user access: any user.
$_GET[‘message’] is not escaped. sirv_get_row_by_id() is accessible for every registered user.
File / Code:
Path: /wp-content/plugins/simple-personal-message/admin/partials/simple-personal-message-admin-view.php
Line: 25
<?php
global $wpdb;
$table = $wpdb->prefix . 'spm_message';
$id = esc_attr($_GET['message']);
$message = $wpdb->get_results("SELECT * FROM $table WHERE id = $id");
$user = get_user_by('login', $message[0]->sender);
?>
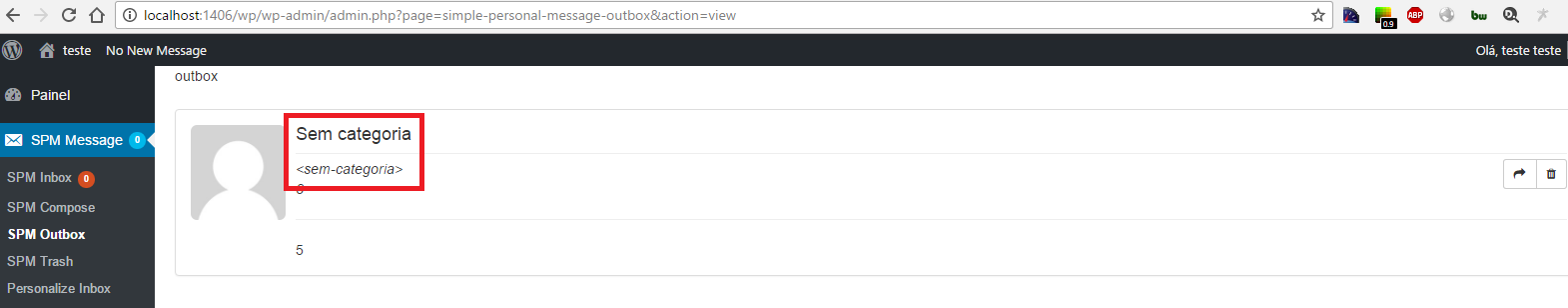
Proof of Concept:
1 – Login as regular user (created using wp-login.php?action=register):
2 – Access url:
Result:
Timeline:
- 28/11/2016 – Discovered
- 28/11/2016 – Vendor notifed
title of blog, ‘Single’ should be ‘Simple’
Thanks man. =)